A home network can look fine on the surface and still create daily frustration. Video calls stutter during uploads. Smart devices sit on the same network as laptops and storage. Remote access feels risky, so it gets postponed again and again. Once a homelab grows past a few connected devices, the router from your internet provider often becomes the weak point. A dedicated firewall changes that picture. It gives you tighter control over traffic, clearer security boundaries, and a better way to manage privacy, performance, and remote connectivity without turning your house into a tiny data center.
Why ISP Routers Fall Short for a Secure Homelab
Provider-supplied routers are built for convenience. They are meant to get a household online quickly, with minimal setup and minimal support calls. That works well for a basic network. It stops working so well when your homelab includes self-hosted services, smart home devices, network storage, media systems, and remote access needs. At that point, you need more than a simple internet gateway. You need policy, visibility, and room to grow.
NAT Is Not a Security Policy
One of the most common misunderstandings in home networking comes from NAT. Many people see it as proof that their network is secure. In reality, NAT translates addresses so internal devices can share one public connection. That function is useful, though it does not decide which systems should talk to each other, which services deserve outside access, or which devices should stay isolated.
A real firewall handles those decisions through policy. It tracks sessions, applies rules by interface or network segment, and gives you a way to control traffic with intent. That difference matters in a homelab. A media server, backup target, laptop, and smart speaker should not all enjoy the same level of trust simply because they sit behind one public IP.
Flat Networks Spread Risk
That is why segmentation belongs near the top of the priority list. Separate networks give you cleaner boundaries, such as:
- a trusted zone for personal computers
- an isolated zone for IoT devices
- a guest network with limited access
- a tighter segment for lab services and management
This design makes access rules easier to manage and reduces unnecessary risk across the network.
Visibility Changes Everything
Performance issues are often harder than security issues because they feel mysterious. The network seems slow, yet nobody knows why. Upload gets saturated, latency jumps, and the only tool available is a vague speed test. Consumer routers rarely explain much.
A dedicated firewall gives you a more useful view of reality. You can see which device is consuming bandwidth, which segment is busiest, and when a service starts behaving oddly. That visibility makes your network easier to fix and easier to trust. It also saves time. Instead of guessing, you can make decisions based on evidence.
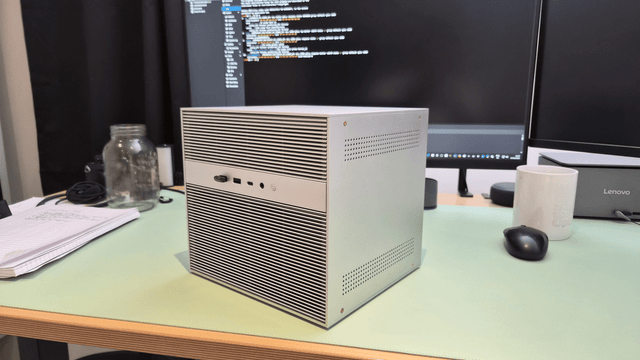
How to Choose the Right Hardware for a Homelab Firewall

The key to choosing firewall hardware is to focus on what your network needs now, while leaving some room for future growth. A good firewall should run reliably every day, handle your main network tasks smoothly, and stay flexible as your homelab expands.
Confirm Your Needs
First, think about how you plan to use the firewall. A small home network with a few devices will not need the same hardware as a setup with VLANs, cameras, remote access, and large file transfers.
Ask yourself a few basic questions:
- How fast is your internet connection?
- How many devices are online every day?
- Do you want a VPN, encrypted DNS, or traffic monitoring?
Choose x86 for Flexibility
For many homelab users, x86 is a practical choice. It supports a wide range of firewall software and gives you more flexibility in the long run. That means you can start with basic routing and security, then add more features later if needed.
This is helpful because most homelabs grow over time. What begins as a simple firewall may later take on extra jobs like DNS filtering, reporting, or other network services.
Prioritize Reliable NICs
The network ports matter more than many buyers expect. A firewall depends on stable, reliable Ethernet connections, so good NICs are important. If the network interfaces are weak or inconsistent, the whole setup can become frustrating to manage.
This matters even more if you plan to use multiple VLANs, several wired segments, or faster local networking. Reliable NICs help the firewall stay stable and make the entire network easier to trust.
Leave Room for Growth
It is smart to avoid buying hardware that only fits your current needs exactly. A firewall often takes on more work over time. You may add a VPN, traffic shaping, more devices, or faster internet later.
A little extra performance headroom helps the system stay smooth and useful for longer. It also saves you from needing an upgrade too soon.
Consider Power Use
A home firewall stays on all the time, so power efficiency matters. You want hardware that is strong enough for the job without wasting energy every day.
The best choice is usually a balanced one: enough performance for your network, enough flexibility for future upgrades, and low enough power use for 24/7 operation. That kind of hardware tends to work best in a homelab.
Best Firewall Operating Systems for a Home Network
The operating system decides how the firewall feels day to day. Some people want an appliance-style interface with rich policy controls and strong built-in networking tools. Others prefer a lean, modular platform that can be shaped piece by piece. Some want the firewall virtualized because the rest of the lab already lives on a host. Each path can work well. The best fit depends on how you like to manage systems and how much complexity your household will tolerate.
Appliance-Style Platforms
A traditional firewall distribution tends to be the easiest fit for people who want clear menus, strong rule control, and a security-first mindset. These systems usually bring together interface management, VLANs, VPN functions, policy routing, logging, and traffic analysis in one place. That makes them approachable without making them simplistic.
For many homes, this model feels natural. You install the system on dedicated hardware, define the internal networks, build rules around trust levels, and manage the edge as a self-contained appliance. It is a clean design that ages well.
Lightweight Modular Systems
A modular routing platform appeals to people who enjoy selecting each service with care. It can stay lean, efficient, and highly customizable. That can be a great fit for users who already know what they want from DNS, DHCP, local filtering, and routing policy.
The tradeoff is operational effort. A modular setup can take a little more planning before it feels polished. Still, for a small homelab with focused needs, that flexibility can be rewarding. You keep only the pieces you value, and the system stays easy to reason about.
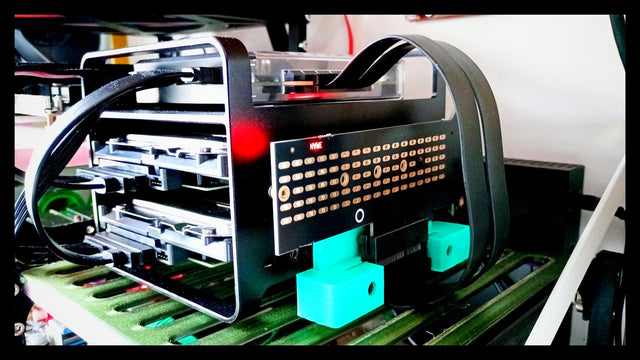
Virtualized Firewalls
Virtualizing the firewall can make a lot of sense inside a lab that already uses a host for storage, containers, or test environments. Snapshots are handy. Hardware utilization improves. Rebuilding or migrating the firewall can become simpler, too.
There is a catch, and it is an important one. Your network edge now depends on a broader stack. If the host goes down, the firewall goes with it. That may be fine for an experimental environment. It may be annoying in a house where internet access supports work, school, and daily routines. The design is valid. It just needs honest expectations.
Core Firewall Configurations Every Homelab Should Have
A strong firewall does not require a giant wall of rules. It needs a few well-chosen controls that solve real problems and remain understandable months later. Good network design comes from clarity. If a rule exists, you should know why it exists. For most homes, the essentials are segmentation, encrypted DNS, and safe remote access. Those three pieces give a homelab a much stronger foundation immediately.
Segment by Trust
Segmentation works best when it reflects real trust levels. Personal computers and phones belong in one zone. IoT devices belong in another. Guests should stay separate. Management access deserves tighter protection than ordinary client traffic.
This approach improves the network in several practical ways:
- It limits lateral movement between devices.
- It reduces unnecessary traffic across segments.
- It makes firewall rules easier to read and maintain.
- It helps keep sensitive services away from low-trust devices.
A camera network should not initiate connections to your storage network, and a guest device should not browse internal services. Once those boundaries are in place, the network becomes calmer and safer.
Encrypt DNS at the Gateway
DNS is one of the easiest parts of the network to overlook. It is also one of the easiest places to improve both privacy and control. When DNS is handled at the gateway, you can centralize policy for every device in the house. That may include encrypted upstream queries, local filtering, safer defaults for family devices, and cleaner records for troubleshooting.
This is a practical improvement: it reduces inconsistent settings across clients and gives you one place to manage behavior. In a busy home network, centralized DNS policy removes a surprising amount of clutter.
Keep Remote Access Private
Remote access should feel safe enough to use regularly. If it feels risky, people avoid it or take shortcuts they later regret. A VPN fixes that by giving you a private path back into the network. You can reach internal services, dashboards, and files without exposing each service directly to the public internet.
That is a major quality-of-life upgrade for a homelab. Administrative tasks become easier from outside the house. Travel becomes less disruptive. Internal services stay internal. Good remote access is one of those features that feels optional until you set it up properly. After that, it quickly becomes essential.
Advanced Traffic Control and Monitoring for Better Network Performance
Security alone does not make a network feel good. Performance does. Many households rebuild their edge because the network feels unstable under load, not because they are chasing abstract security goals. Large uploads collide with video calls. Cloud backups create lag. Streaming and gaming suffer at the same moment. A capable firewall can address those problems through shaping, inspection, and better observability.
Tame Bufferbloat
Bufferbloat is one of the most common causes of a network that feels slow despite decent bandwidth. The problem comes from excess queueing delay, especially during uploads. Traffic shaping helps manage that by controlling how packets are queued and sent. When configured well, it keeps the connection more responsive under load.
The improvement can be dramatic in everyday life. Calls sound cleaner. Gaming feels steadier. Large transfers stop disrupting everything else. This is one of the most practical features a serious home firewall can offer because it directly improves how the internet feels from room to room.
Add Inspection with Care
Traffic inspection can provide helpful insight into what is moving across the network. It can also create false positives if it is deployed too aggressively. That is why gradual rollout makes sense. Build the basic firewall policy first. Understand normal traffic. Then add a deeper inspection in a way that supports stability.
A measured approach protects the household from unnecessary disruption. It also helps you avoid the common trap of enabling advanced features faster than you can manage them. Inspection is valuable, though only when it supports the network instead of creating confusion.
Watch the Patterns That Matter
Monitoring becomes powerful when it answers ordinary questions quickly. Which device is saturating upload right now? Which segment is busiest at night? Is one service suddenly talking far more than usual? Is latency rising during backups or during streaming?
Those answers change how a homelab is run. You can tune the network with confidence, catch odd behavior earlier, and spend far less time troubleshooting by instinct. Good visibility also has a calming effect. Problems stop feeling random when you can actually see them.

Building a Smarter and More Sovereign Homelab Network
A professional-grade home firewall is really about control. You decide how trust is divided, how remote access works, how DNS is handled, and how the network behaves under pressure. That changes the daily experience of running a homelab. The network stops feeling fragile and starts feeling intentional. With sensible hardware, clean segmentation, encrypted DNS, private remote access, and smarter traffic management, your firewall becomes the foundation that makes the rest of the lab easier to secure, easier to manage, and much more pleasant to use.
FAQs
Q1. Do I need to put my ISP router in bridge mode before using a home firewall?
Usually, yes, if your provider allows it. Bridge mode helps avoid double NAT, which can complicate port forwarding, remote access, and troubleshooting. If bridge mode is unavailable, your firewall can still work behind the ISP router, though setup is often less clean and less flexible.
Q2. How much RAM and storage does a homelab firewall actually need?
In many home setups, modest hardware is enough. A basic firewall can run comfortably with light resources, but logs, reporting, VPN use, and extra services increase demand over time. A practical approach is to leave enough headroom for updates, rule growth, and future network visibility tools.
Q3. Should a firewall replace my Wi-Fi router completely?
Not always. In many homes, the cleaner setup is to let the firewall handle routing and security, while a separate access point handles wireless coverage. This gives you better placement, easier upgrades, and more flexibility when you want stronger Wi-Fi without changing the entire network edge.
Q4. Is a fanless firewall box reliable for 24/7 use?
Often, yes, if airflow and workload are reasonable. Fanless systems are appealing because they are quiet and have fewer moving parts. Still, enclosure design, ambient temperature, and sustained load matter. It is smart to check thermal behavior early, especially if your firewall also runs extra services.
Q5. What is the safest way to update a home firewall without breaking the network?
A cautious approach works best. Back up the configuration first, read the release notes, and update during a low-risk time when downtime is manageable. If your platform supports snapshots or quick restore options, use them. That makes rollback much easier if a plugin or package behaves unexpectedly.
Zima Campaign Hub
More to Read
ZimaCube Home Lab Monitoring Guide: From Uptime Kuma to AI Agents
Monitor your home server with Uptime Kuma, Pulse, Proxmox Data Center Manager, or an AI agent to track uptime, backups, VMs, alerts, and avoid...
From Sparcstation to ZimaBlade: A 57-Year-Old Geek’s Self-Hosting Journey
A French admin professional replaced his failed Raspberry Pi 4 with a ZimaBlade 7700, running Debian 13, XFS, and BorgBackup. Full backup server build...

ZimaCube vs DIY NAS: Which One Is Right for You?
Prebuilt NAS or DIY? We break down real costs, setup time, Thunderbolt 4, and maintenance differences to help you decide which build actually fits...












